When the industrial cybersecurity community analyzes the attack chains behind significant OT incidents, one pattern appears with striking regularity: the intrusion began not through a sophisticated zero-day exploit targeting a proprietary industrial protocol, but through a remote access pathway that was inadequately secured, poorly monitored, or never properly decommissioned.
The Colonial Pipeline incident. The Oldsmar water treatment facility attack. Multiple ransomware campaigns that traversed IT/OT boundaries through VPN and remote desktop connections. The common thread is not exotic technical sophistication, it is the exploitation of legitimate remote access infrastructure that was designed for operational convenience but not adequately hardened for the security reality that connects it to.
In 2024 and beyond, industrial remote access is not a peripheral concern in OT security programs. It is a primary attack surface, and one that is expanding as operational requirements drive more connectivity between industrial environments and the external entities that support them: automation vendors, SCADA integrators, original equipment manufacturers conducting remote diagnostics, engineering consultants accessing process data, and corporate IT teams extending enterprise monitoring into OT networks.
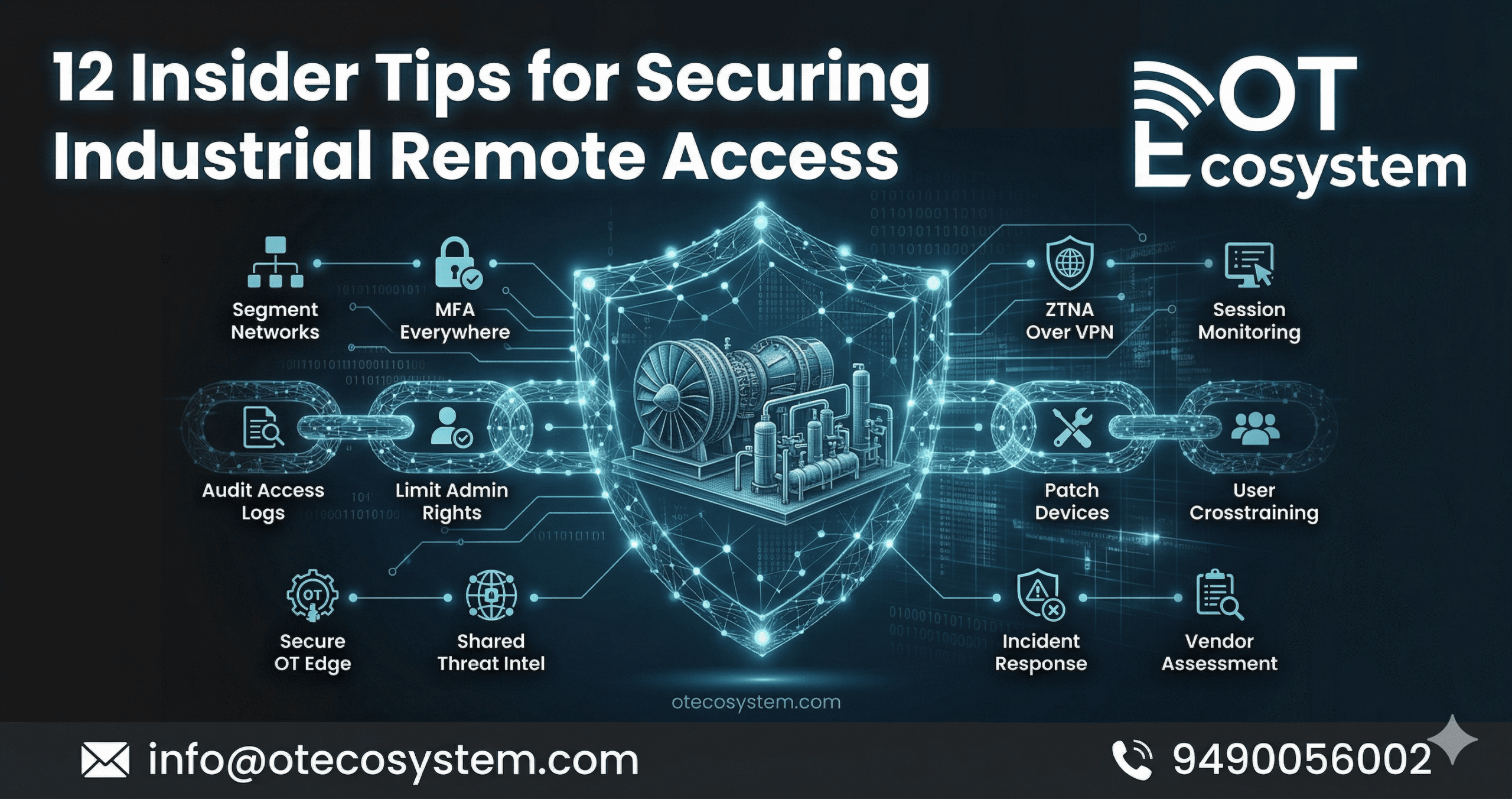
This guide presents the 12 insider tips for securing industrial remote access, practical, operationally grounded controls that security-mature OT organizations are implementing to protect their most exploited attack pathway without compromising the operational functionality that remote access enables.
1. Conduct a Complete Remote Access Inventory Before Implementing Any Controls
What it is: A systematic audit of every remote access pathway into OT systems, VPN connections, remote desktop services, web-based industrial interfaces, vendor-specific remote access tools, cellular-connected RTUs, and any other mechanism that allows external access to the OT environment.
Why it matters in OT: Attempting to secure remote access without knowing what remote access exists is a common and consequential error. Many OT environments have accumulated remote access solutions over years, each implemented for a specific purpose, few of them well-documented, creating an access landscape that security teams cannot protect because they cannot see it.
How it improves security: The inventory provides the authoritative starting point for every subsequent control: you cannot enforce MFA on connections you do not know exist, cannot monitor sessions through pathways outside your monitoring scope, and cannot decommission access you have not identified.
Practical implementation: Combine network traffic analysis, looking for established connections from external IP ranges, with administrative review of all vendor contracts, asset records, and firewall rule sets. The combination of passive discovery and administrative review typically surfaces connections that neither approach would identify alone.
2. Implement Multi-Factor Authentication on Every Remote Access Pathway Without Exception
What it is: Multi-factor authentication requires remote access users to verify their identity through two or more factors, typically a password combined with a time-based one-time password, hardware token, or push notification, before establishing an OT connection.
Why it matters in OT: Credential theft, through phishing, credential stuffing, or compromise of vendor systems, remains the most common way that attackers gain initial access to industrial environments through legitimate remote access channels. MFA eliminates the majority of credential-based attack scenarios by ensuring that stolen passwords alone are insufficient for access.
How it improves security: A remote access environment with MFA requires an attacker to compromise both the credential and the second factor, a significantly higher barrier than credential theft alone. For vendor accounts, which are frequently targeted because they may have access to multiple client environments, MFA protection is particularly critical.
OT-specific consideration: Some legacy remote access solutions do not natively support MFA. In these cases, MFA can often be enforced at the network boundary, through a gateway or jump server that requires MFA before allowing access to the underlying system, rather than within the legacy application itself.
3. Deploy a Dedicated OT Remote Access Gateway or Jump Server
What it is: A jump server or bastion host is a hardened intermediary system through which all remote access sessions must pass, creating a single controlled entry point that enforces authentication, session policy, and monitoring for all remote connections into the OT environment.
Why it matters in OT: Direct remote access to OT devices, bypassing any inspection or control point, is the highest-risk remote access architecture. A jump server creates the chokepoint that makes policy enforcement and session monitoring possible across all remote access regardless of who is connecting or what they are connecting to.
How it improves security: Every remote session passes through the jump server, where authentication is enforced, session recording is initiated, and access controls restrict which OT systems the session can reach. An attacker who compromises remote access credentials still faces the jump server’s additional authentication requirements, network access restrictions, and detection capability.
Scenario: A vendor engineer connects for a scheduled maintenance session. The jump server requires MFA, restricts access to the specific PLC being serviced, records the entire session, and alerts if the connection attempts to reach any system outside the authorized scope, creating both a control and an audit trail in a single architectural component.
4. Implement Just-in-Time Access Provisioning for Vendor and Third-Party Connections
What it is: Just-in-time (JIT) access provisioning creates temporary, time-limited access credentials or connection authorizations that are valid only for specific approved sessions, eliminating the persistent standing access that creates ongoing exposure between actual use occasions.
Why it matters in OT: Persistent vendor credentials, VPN access that is valid 24/7 regardless of whether any maintenance activity is scheduled, represent one of the most common remote access risks in industrial environments. The vendor credential that exists in a perpetual state of readiness is available to an attacker who compromises the vendor’s systems at any time, not just during scheduled maintenance windows.
How it improves security: JIT access eliminates standing access by creating credentials and connection authorizations only when a specific approved maintenance session is scheduled. Outside approved windows, the credentials do not exist, there is nothing for an attacker to compromise.
OT-specific consideration: JIT implementation requires coordination between the security operations team, the relevant engineering or maintenance team, and the vendor, but this operational overhead is typically modest and the security improvement is substantial.
5. Enforce the Principle of Least Privilege for All Remote Access Accounts
What it is: Least privilege access restricts each remote access account to the minimum network access, system access, and command execution permissions required for its specific authorized function, preventing accounts from accessing systems or executing actions beyond their legitimate scope.
Why it matters in OT: Many industrial remote access accounts have been provisioned with broad access that was convenient at the time of initial setup but significantly exceeds what any individual session actually requires. A vendor engineer performing diagnostics on a specific HMI does not need network access to the entire process control network, but if their VPN connection provides it, a compromised credential does too.
How it improves security: Least privilege creates containment, an attacker who compromises a vendor credential can access only what that vendor account was authorized to access, not the entire OT network. For environments with multiple remote access users, least privilege dramatically reduces the potential impact of any individual credential compromise.
6. Record and Monitor All Remote Access Sessions in Real Time
What it is: Session recording captures a complete record of every remote access session, the systems accessed, the commands executed, the files transferred, and any changes made, while real-time monitoring provides the ability to detect anomalous session behavior as it occurs and intervene if necessary.
Why it matters in OT: Session visibility serves two distinct security functions. Forensically, session recordings provide the evidence base for incident investigation, establishing exactly what was done during a session when anomalous activity is discovered after the fact. Operationally, real-time monitoring enables detection and intervention during active sessions that exhibit suspicious behavior.
How it improves security: A remote access environment with comprehensive session recording and monitoring creates a powerful deterrent to both external attackers and insider threats, the knowledge that every action is recorded and reviewed changes behavior. It also provides the detection capability that converts a monitoring program from reactive to real-time.
OT-specific consideration: Session recordings for privileged OT access should be stored securely and retained for a period consistent with both operational and regulatory requirements, not stored on systems accessible to the individuals whose sessions are being recorded.
7. Implement and Enforce Network Segmentation for Remote Access Traffic
What it is: Network segmentation ensures that remote access connections land in an appropriately restricted network zone, typically a DMZ or dedicated remote access segment, from which access to specific OT systems is governed by granular firewall rules rather than broad network access.
Why it matters in OT: Remote access that lands directly on the OT network provides attackers with the same network visibility as local network access, the ability to scan, enumerate, and attempt to reach any networked device. Segmented remote access constrains this visibility to an authorized subset of the OT environment.
How it improves security: Segmentation limits the blast radius of a compromised remote access session. Even if an attacker gains access through a legitimate remote access pathway, segmentation restricts their ability to move laterally to OT systems beyond the session’s authorized scope.
8. Implement Formal Vendor Access Governance Processes
What it is: Vendor access governance establishes formal processes for requesting, approving, provisioning, monitoring, and deprovisioning remote access for third-party vendors and service providers, replacing the informal, ad hoc arrangements that characterize many industrial environments.
Why it matters in OT: Vendor access management is an area where the gap between policy and practice in industrial organizations is frequently large. Access is requested informally, provisioned without documentation, and never formally reviewed or deprovisioned when the need ends, creating an accumulation of standing access that far exceeds what current operational relationships actually require.
How it improves security: Formal governance creates accountability for every access grant, documentation of the business justification, periodic review of whether access remains necessary, and systematic deprovisioning when vendor relationships end or change.
Scenario: An automation vendor completes a major system integration project and the engineer responsible for the engagement leaves the company. Without formal access governance, their credentials may persist indefinitely. With formal governance, access is deprovisioned as part of project closure documentation and vendor employee change notification.
9. Conduct Regular Access Reviews and Deprovisioning Audits
What it is: Periodic structured review of all active remote access accounts and permissions, validating that each account has a current and legitimate business justification, that the access scope remains appropriate, and that credentials are current and not shared.
Why it matters in OT: Access accumulation, the gradual growth of access grants that are never removed because deprovisioning is not systematically tracked, is one of the most common remote access vulnerabilities in industrial environments. Access reviews convert deprovisioning from a reactive activity (responding to known departures) into a proactive one (systematically verifying that all existing access remains appropriate).
How it improves security: Regular access reviews ensure that the remote access landscape reflects current operational relationships rather than historical ones, removing the orphaned credentials that create attack surface without providing any operational benefit.
10. Enforce Strong Password and Credential Management Policies
What it is: Password and credential management policies establish minimum password complexity requirements, maximum credential lifetimes, prohibition of shared credentials, and secure credential storage requirements for all remote access accounts.
Why it matters in OT: Default credentials, unchanged from vendor-supplied factory defaults, remain among the most frequently exploited vulnerabilities in industrial remote access. The additional problem of shared credentials, where multiple individuals use the same account for operational convenience, eliminates both accountability and the ability to conduct meaningful session attribution during incident investigation.
How it improves security: Strong credential management removes the lowest-hanging fruit of credential exploitation while ensuring that session activity can be attributed to specific individuals, both for access control and for forensic investigation purposes.
11. Establish and Test Incident Response Procedures for Remote Access Compromise
What it is: Documented, tested response procedures specifically addressing the scenarios most likely to involve remote access compromise, unauthorized access attempts, anomalous session behavior, and credential compromise notifications, with defined escalation paths, containment actions, and recovery procedures.
Why it matters in OT: Incident response without specific remote access scenarios fails to account for the operational considerations that make OT incident response different from IT, the need to balance security containment with operational continuity, and the safety implications of response actions that affect control system connectivity.
How it improves security: Having pre-tested response procedures ready before an incident occurs dramatically improves both response speed and response quality. The decision about whether to immediately terminate a suspicious vendor session, which may have operational consequences, is better made as a pre-planned policy choice than as an improvised decision under incident pressure.
12. Align Remote Access Security With a Zero Trust Architecture Approach
What it is: Zero trust architecture applies the principle that no remote access connection should be implicitly trusted based on network location or previous authentication, requiring continuous verification of identity, device health, and access authorization throughout the session lifecycle.
Why it matters in OT: The traditional perimeter-based security model, trust everything inside the network, distrust everything outside, has been fundamentally undermined by remote access connectivity that brings external entities inside the network boundary. Zero trust principles restore security by enforcing verification at the access level rather than the network level.
How it improves security: Zero trust approaches require that every access request be explicitly authorized based on current identity verification, device compliance, and least privilege principles, rather than assuming that a previously authenticated session remains trustworthy for its duration.
Conclusion:
The 12 insider tips for securing industrial remote access covered in this guide collectively address the full spectrum of vulnerabilities that make remote access the most exploited OT attack pathway in the current threat landscape. No single control is sufficient; the strength of a remote access security program lies in the layered application of complementary controls that together make exploitation significantly more difficult and significantly more detectable.
For OT security teams assessing their current remote access posture, the most valuable immediate step is the inventory, understanding what remote access exists before attempting to secure it.
Stay Connected With OT Ecosystem
We invite cybersecurity professionals, OT engineers, risk managers, consultants, and industry experts to contribute their knowledge and share actionable perspectives that support safer and more resilient industrial operations.
If you would like to publish your article on this platform or explore opportunities across other leading platforms, please feel free to reach out to us.
📩 Email: info@otecosystem.com
📞 Call: +91 9490056002
💬 WhatsApp: https://wa.me/919490056002
