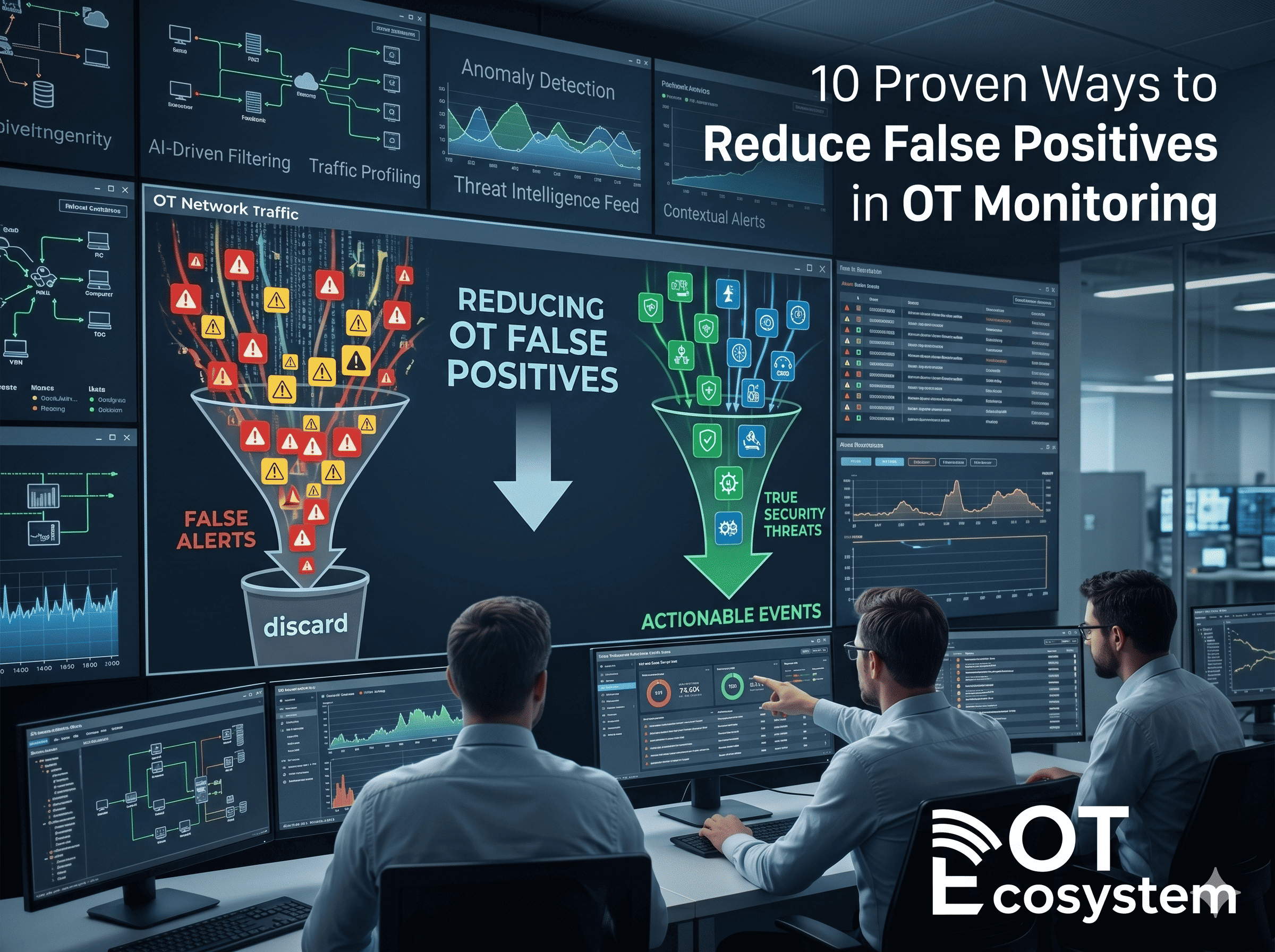
In operational technology environments, alert fatigue is not just a nuisance, it is an operational and security risk. When security systems generate hundreds of alerts daily, many of which...
Penetration testing in enterprise IT environments is a mature discipline with well-established tools, methodologies, and practitioner communities. In ICS and OT environments, the same fundamental objective, finding exploitable vulnerabilities...
The operational technology security landscape has reached an inflection point. Attack surfaces are expanding as legacy industrial systems connect to enterprise networks, cloud platforms, and remote access infrastructure. Threat...
When an industrial incident occurs , whether a ransomware event reaches Level 2 of the control network, an unauthorized configuration change disrupts a production process, or an anomalous communication...
Operational Technology (OT) environments are not the same as corporate IT: they move real material, control hazardous machinery and demand determinism and safety. Yet most OT estates still rely...
You cannot secure what you cannot see. In OT environments, that principle carries physical consequence, an unmanaged PLC running obsolete firmware, an undocumented vendor connection into a safety relay...
Modbus and DNP3 are the workhorses of industrial control. Modbus, designed in 1979, underpins millions of PLC and sensor connections across manufacturing, water, energy, and building automation. DNP3 became...
Visibility is the foundation of industrial cybersecurity. Without an accurate, trusted inventory of Industrial IoT (IIoT) and OT devices you cannot detect compromise, prioritize risk, or safely change anything...
Supervisory Control and Data Acquisition (SCADA) systems are no longer isolated engineering platforms quietly running in the background of industrial facilities. They are connected, monitored, remotely accessed, cloud-integrated, and...
Why Converged Monitoring Has Become an Industrial Necessity Industrial cyber incidents no longer respect the boundary between IT and OT. Over the past decade, adversaries have demonstrated-repeatedly-that initial access...